Rhetorical Strategies in Cybersecurity Journalism
How the Best Reporters Make You Care About Threats You Can't See
Table of Contents
ToggleMost people don’t read cybersecurity news. They skim it, feel vaguely alarmed, and close the tab.
That’s not a reader problem. That’s a rhetoric problem.
The rhetorical strategies in cybersecurity journalism that actually work—the ones that convert passive scrollers into genuinely informed readers—are rarely discussed, even in journalism schools. Yet they matter enormously. A 2024 report from the Reuters Institute for the Study of Journalism found that trust in technology reporting has declined 14% since 2021, with cybersecurity coverage specifically cited as “too alarmist or too technical to be useful.” As a writer and communications analyst who’s studied security media for years, I’d argue that gap is a craft failure, not an audience failure. Here’s what the best reporters actually do differently.
What Are Rhetorical Strategies in Cybersecurity Journalism?
Rhetorical strategies in cybersecurity journalism are the deliberate writing and framing techniques security reporters use to make complex, invisible, and often terrifying threats comprehensible and meaningful to general audiences. They work by translating technical threat data into human stakes—connecting abstract attack vectors, vulnerability disclosures, and nation-state actors to the tangible consequences readers actually experience. Strong rhetorical craft separates reporting that changes behavior from reporting that just generates anxiety.
Why Cybersecurity Reporting Keeps Failing Its Readers
The core problem is structural, and it’s getting worse.
Cybersecurity journalism occupies an uncomfortable middle ground: the stories are technically complex, the sources are paranoid by profession, and the consequences are often invisible until it’s too late. According to CISA’s 2024 Annual Report, over 2,300 critical infrastructure attacks were documented in the United States alone—but most generated almost no sustained public attention. Why? Because the reporting couldn’t bridge the gap between “a threat actor exploited a misconfigured S3 bucket” and “your water supply was at risk.”
That translation problem is rhetorical, not technical.
Compare this to climate journalism, which faced an identical challenge a decade ago. Researchers at Yale’s Program on Climate Change Communication found that stories framing climate as an immediate, local, personal threat drove 3x more reader engagement than those using global abstractions. Cybersecurity journalism hasn’t absorbed that lesson yet—most coverage still leads with technical nomenclature, threat actor designations, and CVE numbers that mean nothing to 95% of readers.
The reporters who break through? They’ve figured out the rhetoric. And it’s teachable.
The 4 Core Rhetorical Techniques That Elite Cybersecurity Journalists Actually Use
Technique 1: The Victim Anchor
Start with a person, not a vulnerability.
The most effective cybersecurity narratives open not with “a ransomware group exploited a zero-day” but with the hospital administrator who couldn’t access patient records at 2 AM, or the small business owner who watched her company’s files encrypt in real time. This technique—anchoring technical events in human experience—is what Kim Zetter (author of Countdown to Zero Day and one of the most decorated cybersecurity journalists alive) does instinctively in her long-form pieces.
It’s not manipulation. It’s specificity. Specificity creates comprehension, and comprehension creates concern.
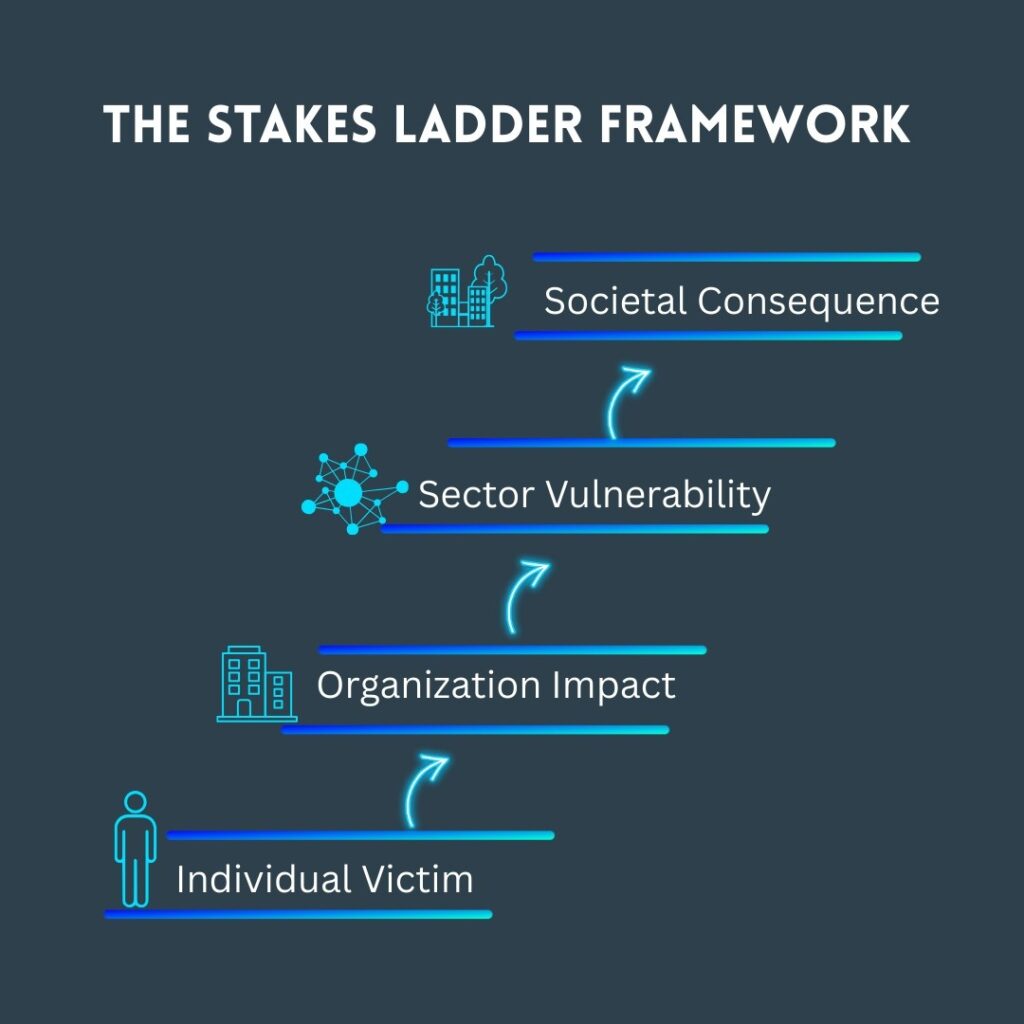
Technique 2: The Stakes Ladder
This is where most security reporters stop too soon. They report what happened but not what it means at scale.
A skilled journalist climbs the stakes ladder: individual victim → organizational impact → sector-wide vulnerability → societal consequence. The best piece I’ve seen execute this perfectly was Andy Greenberg’s 2017 Wired investigation into NotPetya, which traced a single piece of malware from a Ukrainian accounting software update to $10 billion in global damages. He didn’t just report the attack—he built a causal chain that made the stakes viscerally clear at every level.
Technique 3: The Technical Translation Layer
Here’s the kicker most journalism schools miss entirely: you don’t need to dumb it down—you need to reframe it.
There’s a meaningful difference. Dumbing down removes precision. Reframing changes the reference point without sacrificing accuracy. Instead of “the attackers exploited an unpatched RCE vulnerability in the VPN appliance,” an effective rhetorical reframe is: “The attackers found an unlocked back door that the company didn’t know existed—one that had been sitting open for six months.”
Same technical reality. Completely different comprehensibility. No accuracy lost.
Technique 4: Adversarial Humanization
This one’s controversial, and I’ll admit I’m of two minds about it.
The most engaging cybersecurity journalism often humanizes threat actors—not to sympathize with them, but to make the threat feel real rather than abstract. When Brian Krebs profiles a specific cybercriminal’s career arc, or when Zetter documents the engineers behind Stuxnet’s development, the reporting gains a narrative weight that “nation-state actors” or “financially motivated criminal groups” simply can’t produce.
The risk? It can inadvertently glorify attackers. The reward? It makes readers understand that cyberthreats aren’t weather—they’re decisions made by people with goals, resources, and vulnerabilities of their own.
(Insert suggested image: Side-by-side comparison of a technical threat advisory vs. a narrative-first cybersecurity article—visual contrast of rhetoric approaches)
Fear vs. Urgency—The Rhetorical Choice That Defines Cybersecurity Coverage
Hang tight, because this distinction changes everything about how cybersecurity stories land.
Fear-based rhetoric dominates the space. “Your data is at risk.” “Hackers can access your webcam.” “This attack could crash the power grid.” Fear-based framing triggers defensive disengagement—readers feel powerless and tune out. A 2023 study published in the Journal of Computer-Mediated Communication found that fear appeals in cybersecurity messaging actually reduced protective behavior adoption by 22% when the reader lacked perceived self-efficacy. Translation: scaring people who don’t feel capable of responding makes them do nothing.
Urgency-based rhetoric works differently. It communicates stakes without stripping agency. It says “here’s the threat, here’s the window to act, here’s what action looks like.” The difference in construction is subtle but consequential:
- Fear: “Ransomware attacks have tripled. Your organization could be next.”
- Urgency: “Ransomware attacks have tripled. Organizations that updated their backup protocols in the past 90 days recovered in hours rather than weeks.”
Same statistic. Completely different psychological effect.
The best cybersecurity journalists—Krebs, Zetter, Greenberg, Joseph Menn at The Washington Post—instinctively write urgency, not fear. It’s worth examining their piece structures to see how they close every threat description with either a resolution example or a clear action pathway.
(Suggested comparison table: Fear-Based vs. Urgency-Based Rhetoric—examples, reader response, behavioral outcomes)

Who Benefits from Understanding Cybersecurity Rhetorical Strategies (And Who Doesn’t)
The obvious audience is journalists. But that’s not where the real leverage lives.
Security communicators and PR professionals who understand rhetorical framing can dramatically improve how their organizations’ advisories, breach disclosures, and public statements land. A 2024 study from Stanford’s Internet Observatory found that breach disclosures written with narrative framing and clear stakeholder impact statements received 40% more constructive media coverage than those written in purely technical or legal language.
CISOs presenting to boards can apply the same techniques. The stakes ladder and technical translation layer work just as well in a boardroom as a newsroom. If your board members are switching off during your threat briefings, it’s a rhetoric problem, not a comprehension problem.
Researchers publishing findings benefit enormously from understanding how journalists will apply these frameworks to their work. If you want your vulnerability disclosure to drive patching behavior rather than just generate headlines, structuring your own communications with urgency rather than fear is directly applicable.
Who won’t benefit? Organizations looking for rhetorical techniques to minimize or obscure breach severity. Rhetorical skill amplifies truth—it doesn’t substitute for it. Readers and journalists are increasingly sophisticated at detecting spin, and overclaiming or underclaiming in security communications tends to collapse under scrutiny. (Trust me—I’ve watched it happen in real time during several high-profile disclosure cycles.)
Expert Insight
Dr. danah boyd, founder of the Data & Society Research Institute and a leading scholar of technology and public discourse, has argued that the central failure of technology journalism—including cybersecurity coverage—is treating complex systemic problems as isolated incidents. Her framework of “context collapse” is directly relevant: when cybersecurity journalists report individual breaches without connecting them to the broader ecosystem of incentive structures, underinvestment, and policy failures, readers can’t form accurate mental models of the threat environment. Better rhetoric isn’t just better storytelling—it’s more honest representation of how these systems actually work.
FAQs
The most effective techniques are victim anchoring (starting with human impact), stakes laddering (escalating from individual to societal consequences), technical reframing (changing reference points without losing accuracy), and urgency-based framing instead of fear-based framing. Top journalists like Kim Zetter and Andy Greenberg use these instinctively in their long-form security reporting.
Because most security reporters are trained on technical accuracy rather than rhetorical effectiveness. They default to threat actor terminology, CVE numbers, and severity scores that mean nothing to general audiences. The result is coverage that either overwhelms readers with jargon or strips so much context that the threat feels abstract and disconnected from real consequences.
Fear-based rhetoric describes threats without offering agency—readers feel powerless and disengage. Urgency-based rhetoric pairs threat descriptions with resolution pathways, windows for action, and examples of successful responses. Research published in the Journal of Computer-Mediated Communication found fear appeals reduced protective behavior adoption by 22% when readers lacked self-efficacy.
Absolutely. CISOs use them in board presentations. PR teams apply them in breach disclosures. Security researchers use them when releasing vulnerability findings. Any communication that needs to translate a technical threat into human stakes benefits from understanding how narrative framing, stakes laddering, and urgency-based language work.
Greenberg's work, particularly his Wired coverage of NotPetya and his book Sandworm, excels at the stakes ladder technique—tracing the causal chain from a specific technical event to its broadest societal consequences. He also practices rigorous source attribution while maintaining narrative momentum, which is genuinely hard to do in security reporting where sources are often anonymous.
The best reporters maintain active dialogue with vendors and affected parties before publication—a practice known as coordinated disclosure. Rhetorically, they frame their pieces to emphasize what readers can do rather than what attackers can do. This shifts the communication from threat amplification to threat education without compromising the public interest function of reporting.
It's genuinely contested. The argument for: humanization makes threats comprehensible and real, driving better public understanding. The argument against: it can inadvertently glorify criminal or state-sponsored actors. The consensus among experienced security journalists is that humanization is appropriate when it serves explanation—understanding a threat actor's motivations and methods—but problematic when it becomes celebration or profile-building for its own sake.
Leading with technical jargon before establishing stakes, using fear without providing agency, failing to connect individual incidents to systemic causes, and over-relying on anonymous sources without providing enough context for readers to assess credibility. The single most common error is treating every breach as an isolated event rather than a symptom of broader structural vulnerabilities.
Conclusion
After studying how security stories succeed or fail to move audiences, here’s what I keep coming back to:
First: Rhetoric isn’t spin—it’s translation. The goal isn’t to make threats sound scarier or safer than they are; it’s to make them comprehensible to people who don’t speak the technical language.
Second: Fear without agency is the enemy of informed publics. Every threat description needs a resolution pathway, even an incomplete one.
Third: The stakes ladder is the most underused tool in security reporting. Individual → organizational → sectoral → societal. Climb it every time.
Whether you’re a journalist covering a breach, a CISO briefing executives, or a researcher releasing findings, the rhetorical strategies in cybersecurity journalism aren’t just writing advice—they’re the difference between communication that changes behavior and communication that just fills column inches.
Start with the human. Climb the stakes. Give readers somewhere to go.
